| Key Points | Details to Remember |
|---|---|
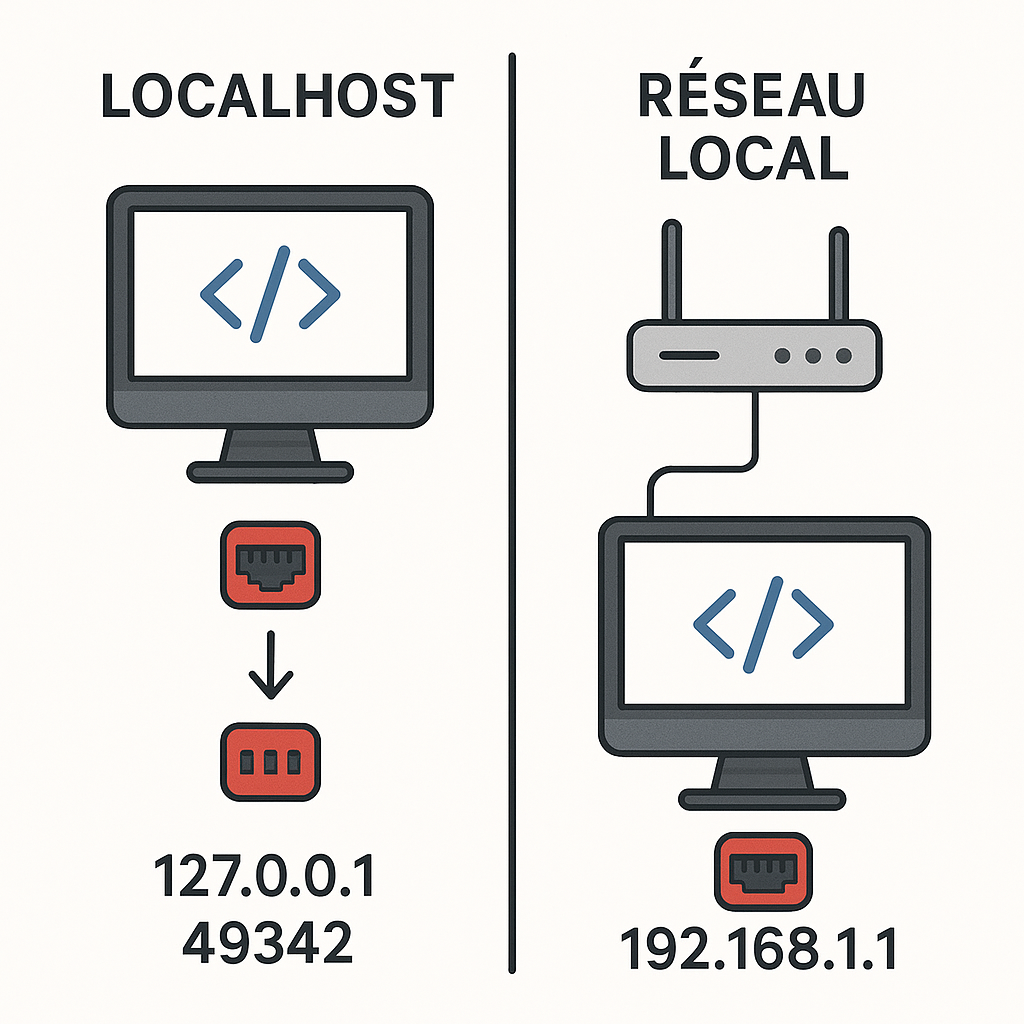
| 📌 Localhost vs local network | 127.0.0.1 remains confined to the machine, 192.168.1.1 serves the entire LAN |
| 🛡️ Security | Increased isolation on localhost, higher risks on LAN |
| 🚀 Performance | Minimal latency locally, slight drop on the network |
| 🛠️ Configuration | Port, firewall and forwarding to fine-tune |
| 🔍 Diagnostics | Tools like netstat, tcpdump or nmap are essential |
| 🔑 Best practices | Authentication, encryption and VPN depending on context |
Choosing an IP address and port to test your web applications often appears as a technical detail. Yet, this decision directly affects the attack surface, ease of debugging, and workflow efficiency. Between the isolation offered by 127.0.0.1:49342 and the inherent openness of 192.168.1.1, the question deserves a methodical and pragmatic approach.
Sommaire
Understanding 127.0.0.1 and 192.168.1.1
Origins and respective roles
127.0.0.1, often referred to as localhost, serves as a loopback: all traffic passes through it without ever leaving the machine. In contrast, 192.168.1.1 often acts as a gateway for a local network, assigned by default to many home routers. When launching a development server on 127.0.0.1, you ensure that no external requests can access it, except via expressly configured tunnels or proxies.
Portability and usage context
Assigning a port — for example 49342 — to your server on localhost allows multiple simultaneous instances without conflict. On 192.168.1.1, you can also choose non-standard ports to evade automatic scanners, but this choice becomes especially relevant when colleagues or external testing tools need to access the application.
Port security in development
Why the port matters so much
The port number defines the entry point to your application. A default or low port (between 0 and 1023) can be filtered or reserved for a system service, while a high port is less targeted by generic scanners. In a local dev context, opting for a random port like 49342 reduces collision risks and decreases visibility to automated intruders.
Exposure and unauthorized access
On 192.168.1.1, any device on the network can send requests. Without authentication or filtering, the attack surface expands. Internally, a simple malicious script on an unprotected workstation could map your services. Conversely, localhost naturally isolates this risk — but remain vigilant if you open an SSH tunnel or a reverse proxy, as isolation then breaks.
Practical comparison
Advantages of 127.0.0.1:49342
- Restricted access to the local machine.
- Default limitation of network vulnerabilities.
- Multiple instances possible by simply changing the port.
- More responsive debugging, less latency.
Strengths of 192.168.1.1
- Easy sharing with colleagues or mobile devices.
- Testing on a network simulating an internal production environment.
- Usable to validate CORS policies or gateways.
- Convenient for testing IoT or connected apps.
Configuring your environment for greater safety
Choosing coherent ports
Favor ports above 1024 to avoid root rights and reserved services. If you switch often, a bash script or a utility like pm2 can automatically reserve free ports while logging history to facilitate diagnostics.
Recommended tools and methods
Netstat and ss provide an immediate overview of occupied ports. For advanced scanning, nmap can detect open services and their versions. In a collaborative context, Consul or etcd help dynamically manage addresses and ports, reducing conflicts and ensuring centralized visibility.
Best practices and recommendations
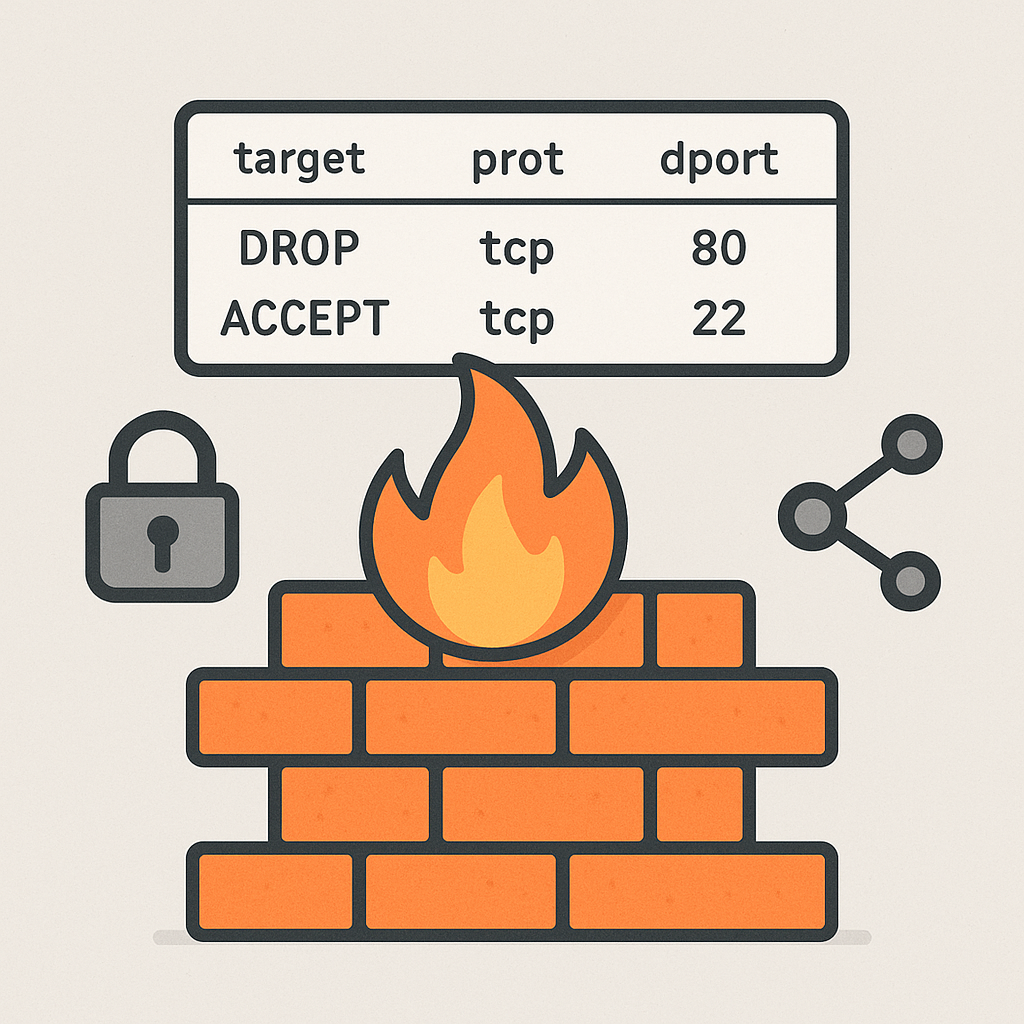
Authentication and firewall
Never leave a port open without controls. Even locally, a firewall such as ufw or iptables can protect you against unsolicited access. On 192.168.1.1, restrict access to trusted subnets or configure a reverse proxy with JWT authentication to lock down each request.
Encryption and tunnels
For sensitive data, simple HTTP on localhost may suffice, but once you venture onto the LAN, you switch to HTTPS. OpenSSL allows you to easily generate a self-signed certificate. If you need external access, an SSH tunnel or VPN (WireGuard, OpenVPN) ensures that traffic remains encapsulated and encrypted.
FAQ
1. Can I use 127.0.0.1 and 192.168.1.1 simultaneously?
Yes, just launch two instances of your server on different ports. This allows you to test locally and on the internal network without conflict.
2. How to quickly find an available port?
Commands like lsof -i or ss -tulpn list listening ports. You can also write a script that tries to open a socket on port ranges and returns the first free one.
3. Should I encrypt my streams even in development?
If your data is sensitive or if you simulate a production environment, yes. A self-signed certificate via OpenSSL combined with an HTTPS configuration is sufficient in most cases.
4. What are the risks if I forget to close a port?
A service left listening can be detected by an attacker, even on a corporate LAN. Without real-time updates or patches, the application becomes a potential entry point for ransomware or a backdoor.
